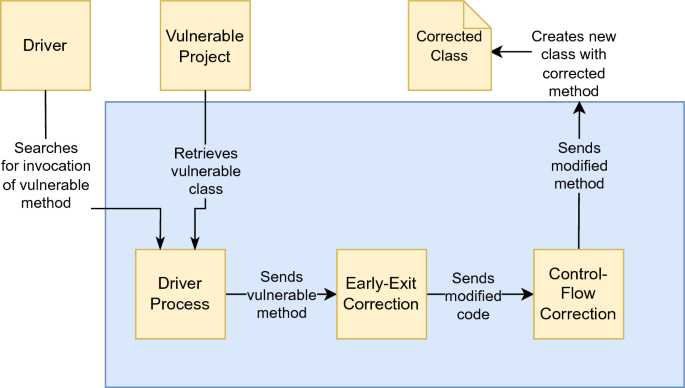
DifFuzzAR: automatic repair of timing side-channel vulnerabilities via refactoring | Automated Software Engineering
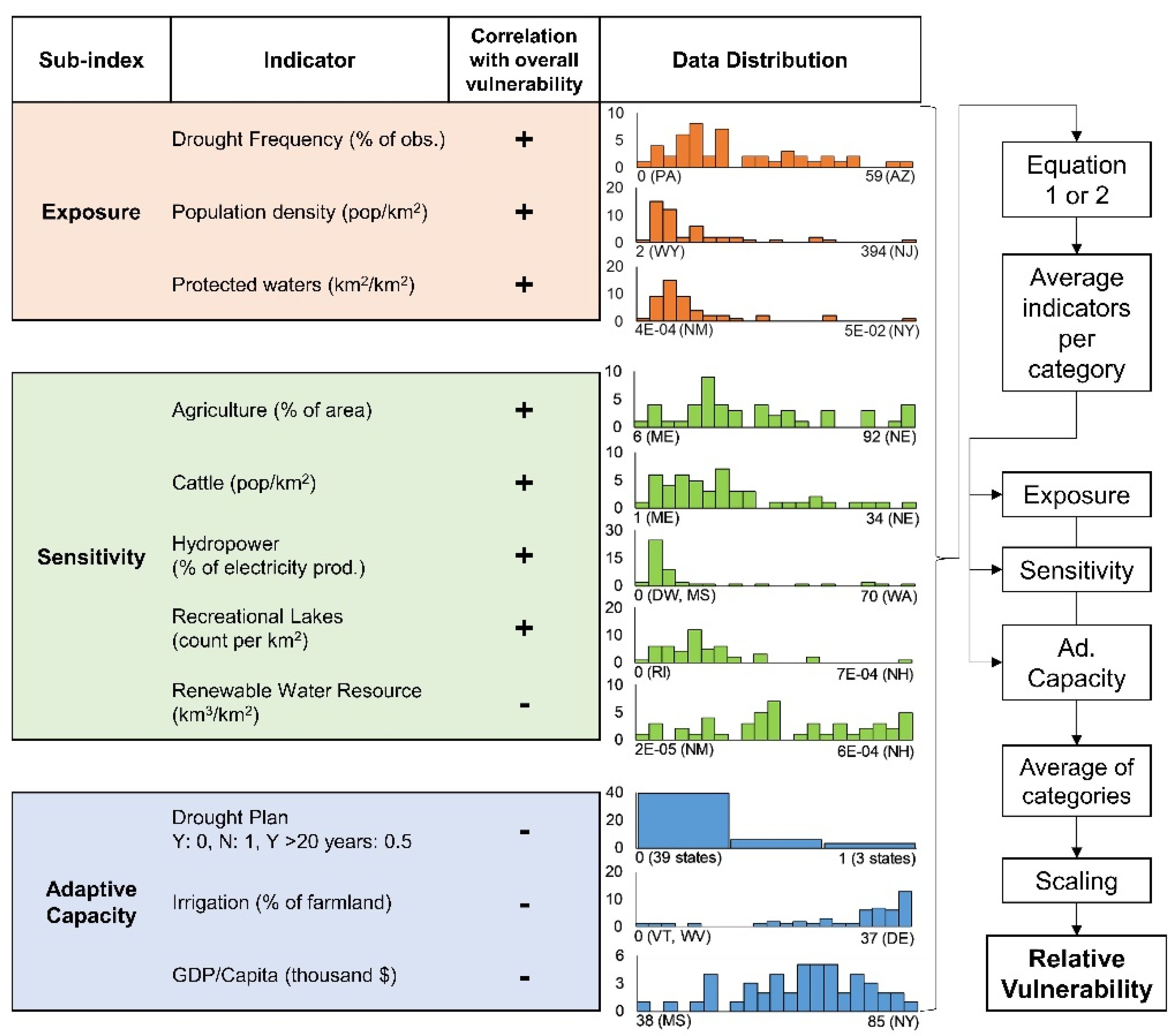
Water | Free Full-Text | Correction: Engström, J., et al. Drought Vulnerability in the United States: An Integrated Assessment. Water 2020, 12, 2033

Fixing a security vulnerability in the system. Cyber security and corporate data protection. Error correction. Hacker attack. Malfunction, breakdown, out of order. Requiring a replacement. Stock Photo | Adobe Stock

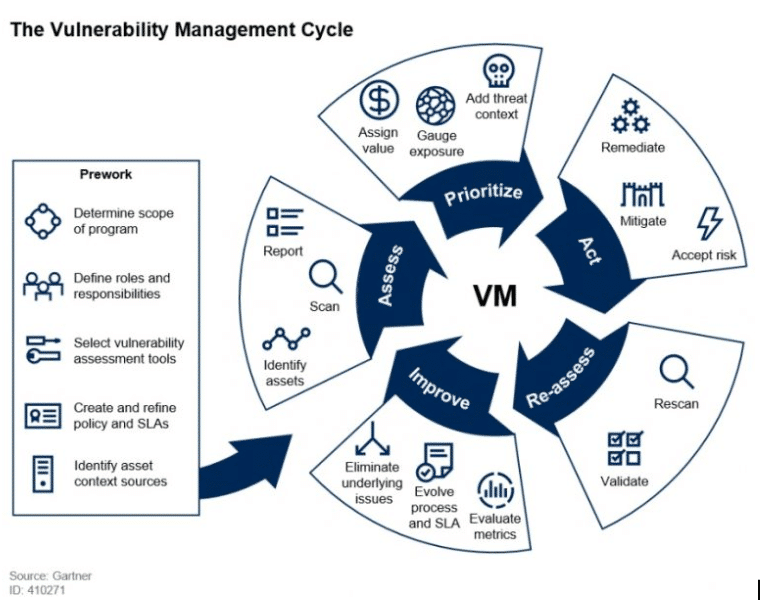
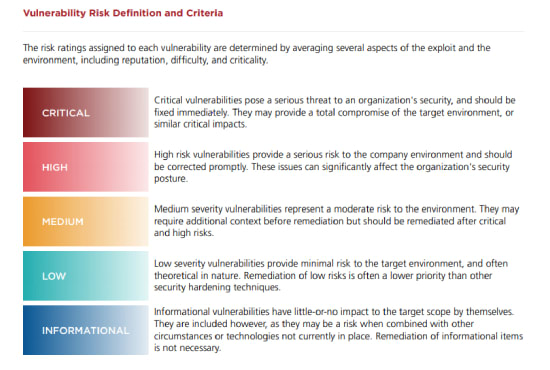
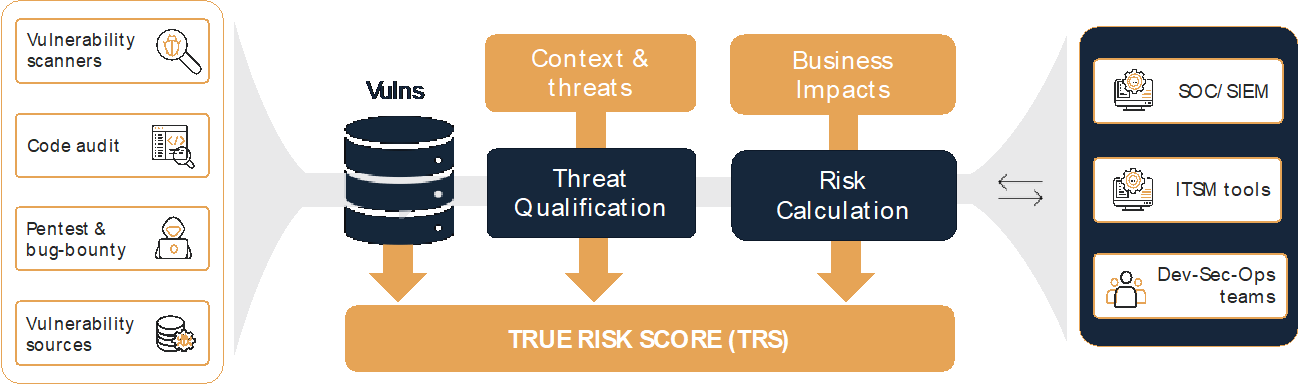
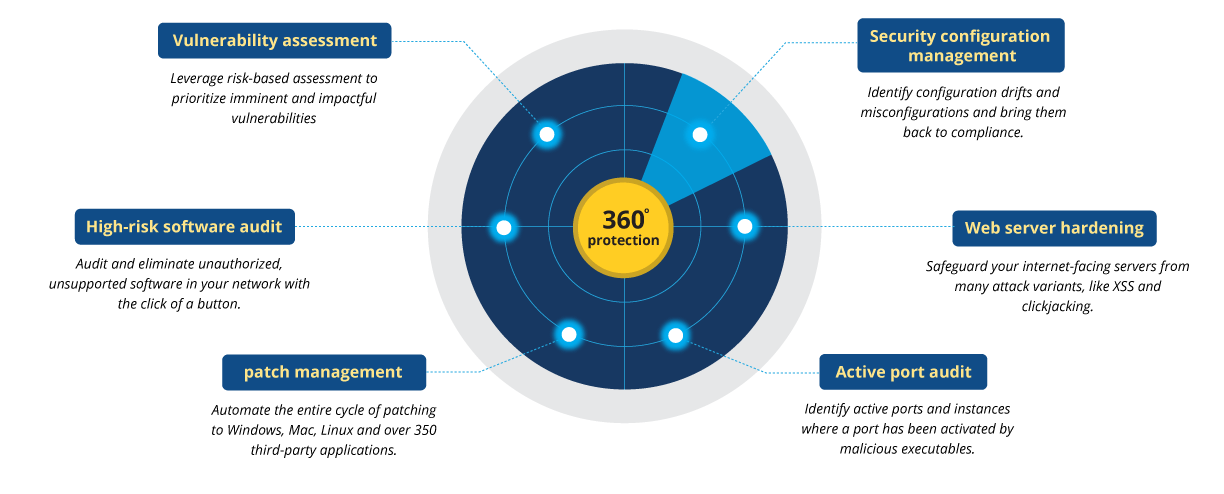
Managing vulnerabilities of information systems and information processing in enterprises – CISO practical point of view | TECH&DEV&SEC - technology, development & security
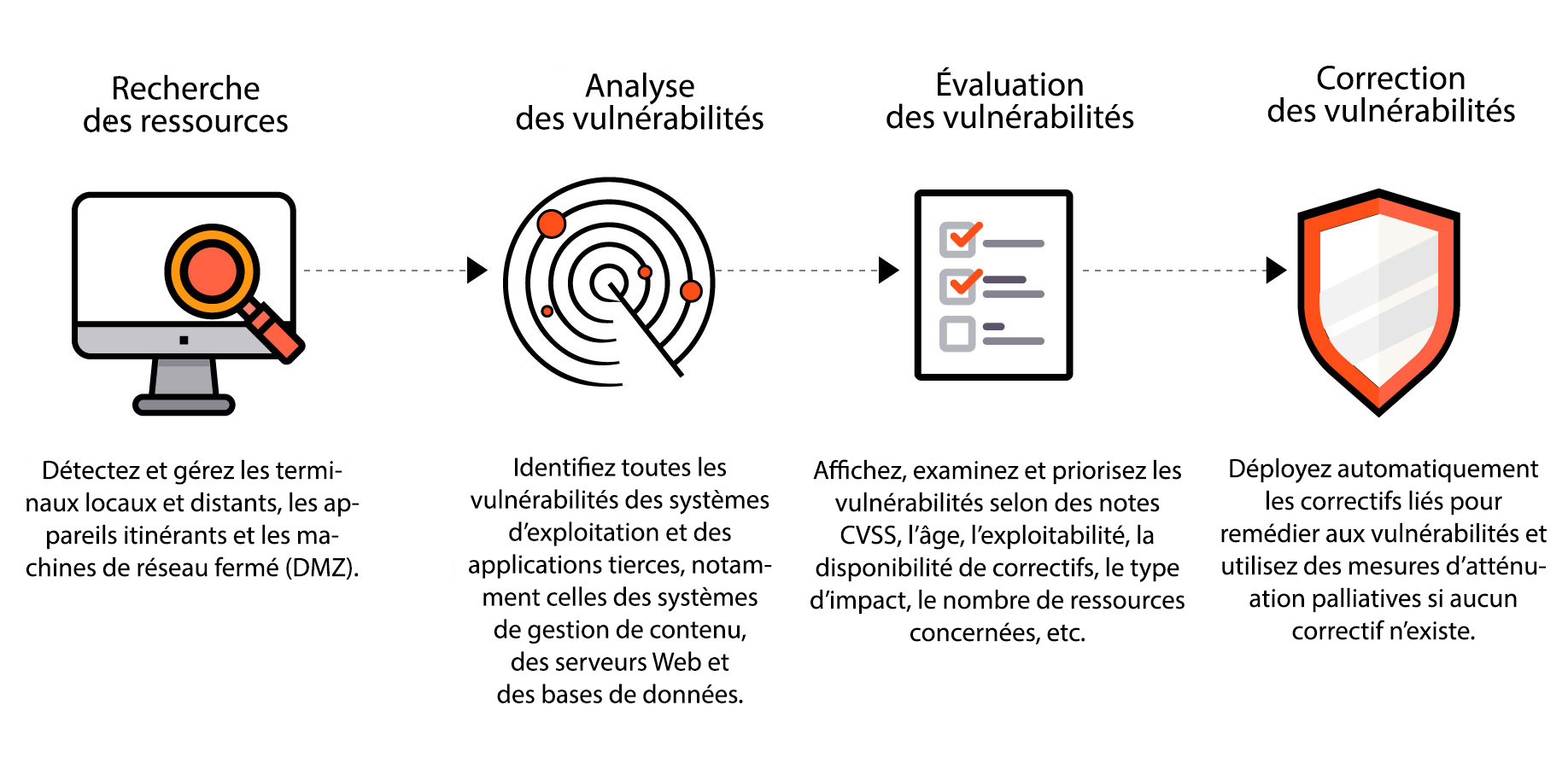
Analyse des vulnérabilités | Outil d'analyse des vulnérabilités - ManageEngine Vulnerability Manager Plus
Définition de la gestion des vulnérabilités | Processus de gestion des vulnérabilités - ManageEngine Vulnerability Manager Plus
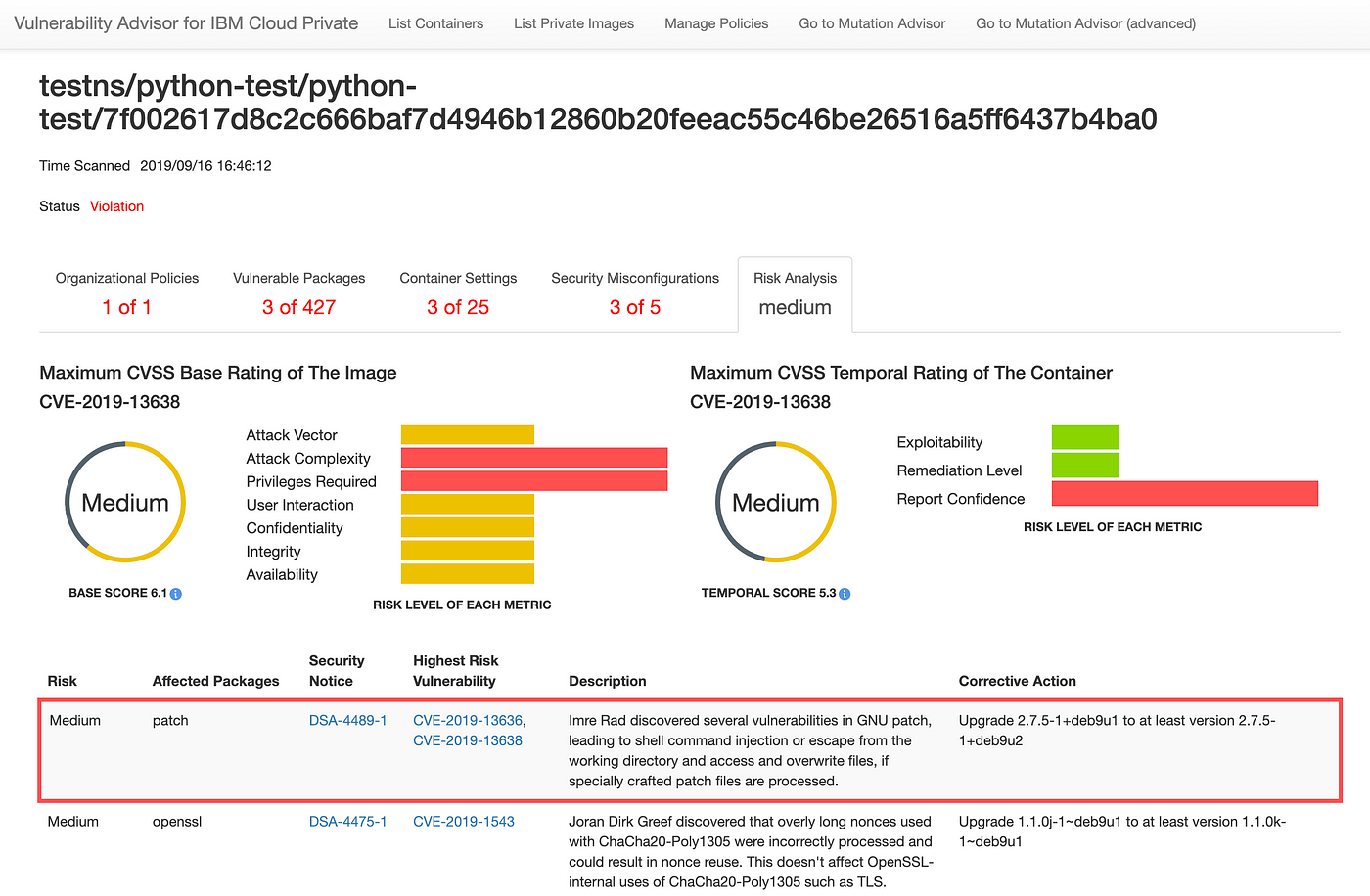
Assessing security risk of your containers with Vulnerability Advisor | by Yuji Watanabe | IBM Cloud | Medium